How HPP Attacks Work
HPP stands for HTTP Parameter Pollution. The HTTP protocol allows the same parameter name to appear multiple times in a request, and attackers exploit this by sending multiple parameters with the same key but different values. This can bypass certain security checks and parameter validation. It’s an injection-type vulnerability where attackers insert specially crafted parameters into HTTP requests to launch an attack.
Here’s a real-world example:
In 2015, someone discovered an HPP vulnerability in HackerOne’s social sharing button.
The vulnerability report showed that modifying the URL:
https://hackerone.com/blog/introducing-signal
to:
https://hackerone.com/blog/introducing-signal?&u=https://me.ursb.me
would cause the social sharing link to become:
Here, the last u parameter takes higher priority than the first. When sharing on Facebook, users would be redirected to https://me.ursb.me instead of HackerOne.
Let me put together a small demo to illustrate this more concretely:
const express = require('express')
const bodyParser = require('body-parser')
const app = express()
app.use(bodyParser.json())
app.post('/login', (req, res, next) => {
const { account } = req.body
return res.json({ message: `login sccessful: ${account}` });
})
app.listen(3000)Say a user types “airing” in the frontend and intends to log in as airing. But the request is tampered with — two account parameters are sent, one with value airing and one with ursb. Without backend validation, the server ends up logging in ursb instead:
POST /login HTTP/1.1
Host: localhost:3000
Content-Type: application/json
{
"account": "airing",
"account": "ursb"
}HTTP/1.1 200 OK
X-Powered-By: Express
Content-Type: application/json; charset=utf-8
Content-Length: 35
ETag: W/"23-/iZ+yuhJ7IhuWOkYuK395opzCZI"
Date: Thu, 11 Apr 2019 13:09:53 GMT
Connection: close
{
"message": "login sccessful: ursb"
}Preventing HPP
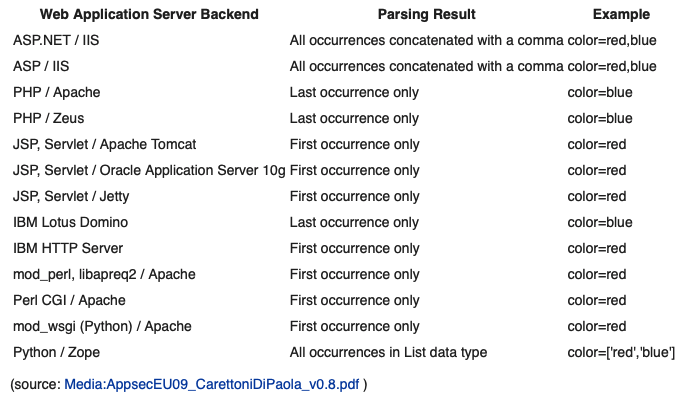
How HPP behaves depends entirely on how the server handles multiple parameters with the same name. Different servers handle it differently:
Keep in mind that the HTTP protocol does allow duplicate parameter names. Throughout the entire request processing pipeline, developers should be aware of this and handle such cases correctly based on their application’s business logic. The most important defense against HPP is thorough backend validation of all input parameters.